PuTTY Home - Free Downloads, Tutorials, and How-Tos
PuTTY is a versatile terminal program for Windows. It is the world's most popular free SSH client. It supports SSH, telnet, and raw socket connections with good terminal emulation. It supports public key authentication and Kerberos single-sign-on. It also includes command-line SFTP and SCP implementations.
Contents
PuTTY downloads Alternative SSH clients How to get an SSH server Tutorials, how-tos, and user manual Features Terminal window Transferring files Public key authentication Telnet support Known security vulnerabilities History and maintenance status Where to find the source code Extensions, branches, and integrations Videos and screenshows Tutorial video Terminal window SFTP clientPuTTY downloads
PuTTY is most commonly used on Windows. It is also available on Linux.
Alternative SSH clients
There many SSH clients that are more modern. A major shortcoming of PuTTY is that it does not have integrated file transfers in the client itself. Instead, file transfers have to be done via the command line. This is too complicated for most users. Tectia SSH has had them since 2000. PuTTY also does not include an SSH server.
How to get an SSH server
PuTTY does not come with an SSH server. It can be used with Linux OpenSSH. For Windows and IBM z/OS mainframes, we recommend the Tectia SSH server.
Tutorials, how-tos, and user manual
Features
-
Windows client. Mac and Linux ports exist. No server included.
-
Supports both 32-bit and 64-bit Windows. An MSI installer has been available since 2016.
-
Supports SSH client, telnet client, SFTP client (command line only), and rlogin client. Both SSH2 and SSH1 protocols are supported. Note that use of SSH1 is not recommended for security reasons. Practically all devices support SSH2 these days.
-
Supports public key authentication and Active Directory/Kerberos authentication.
-
File transfers only using a separate command-line programs. No integrated file transfer support.
-
No scripting support, but can be used together with WinSCP.
Terminal window
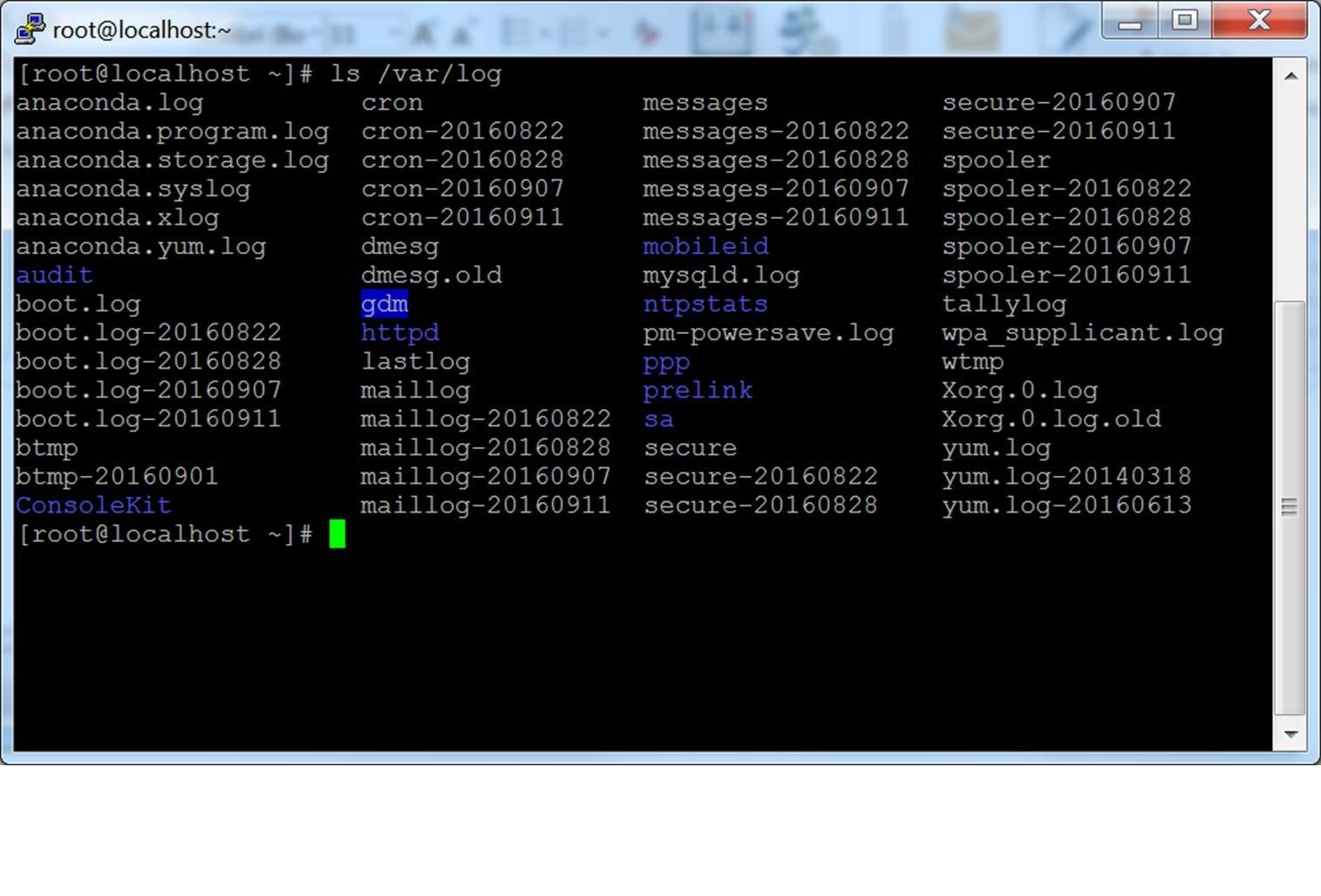
The main feature of the product is the terminal window. It has good terminal emulation, good configurability, and good support for different cryptographic algorithms. SSH, telnet, and plain TCP/IP protocols are supported.
The PuTTY terminal is pretty good and handles terminal emulation well.
Transferring files
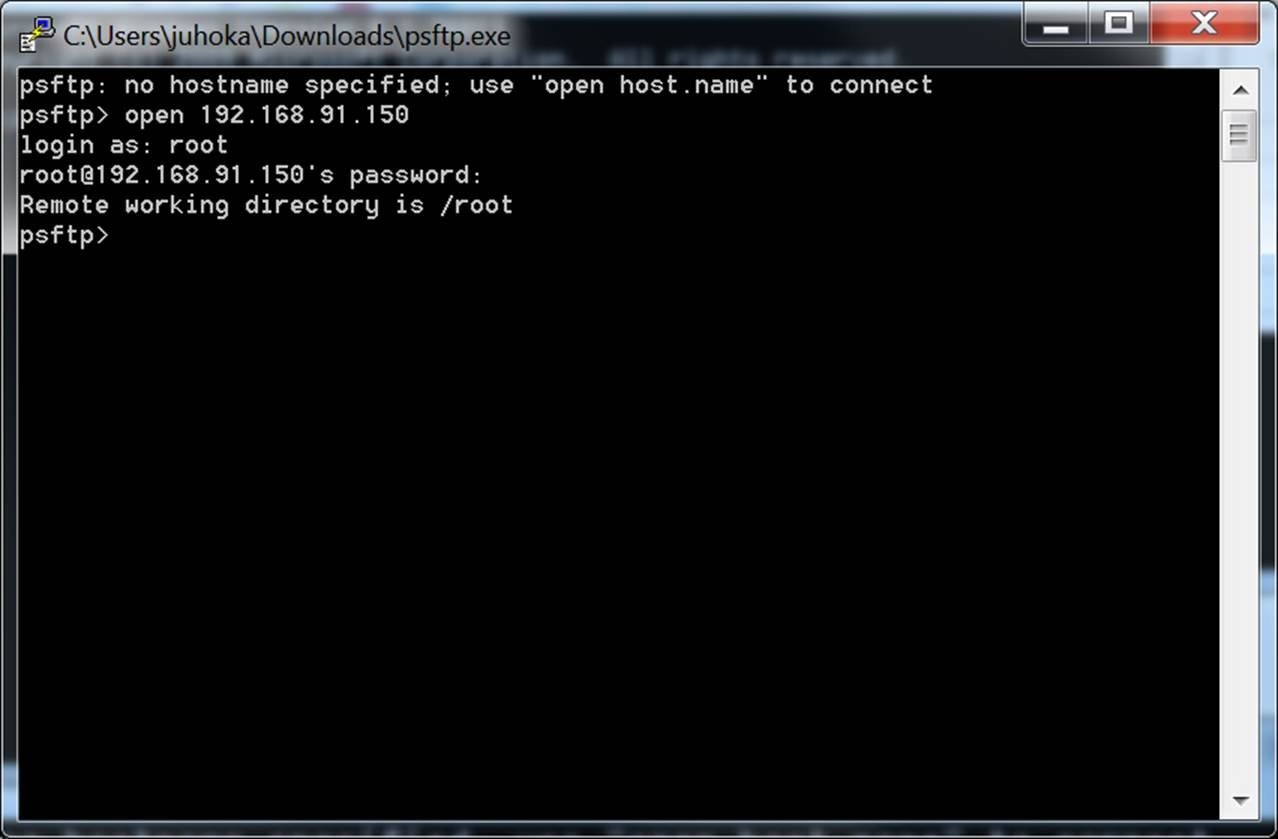
The user interface does not include an integrated file transfer client. However, command-line tools called PSFTP and PSCP are provided. These can be used for file transfers. However, most non-technical users are not willing to use a command line. Tectia SSH, for example, has offered fully integrated file transfer capability since 2000.
The WinSCP and FileZilla clients can also be used for file transfers in conjunction with PuTTY. Having two software packages, switching between them to do operations, and managing profiles and logins for both is extra trouble. WinSCP can now import PuTTY profiles, but separate login is still required for each.
Public key authentication
PuTTY uses its own file format for SSH keys. The keys are stored in .ppk files. The PuTTYgen tool can be used for generating new keys and converting between .ppk files and other key formats.
It is common for hackers and malware to collect SSH keys when penetrating an organization. This happened, for example, in the infamous Sony breach. Recently, Wikileaks obtained CIA hacking tools designed to steal SSH keys and their passphrases.
Managing SSH keys properly is important. Universal SSH Key Manager a popular SSH key management solution and the only one at the time of this writing that supports .ppk files.
Telnet support
PuTTY grew out of a telnet client. It still supports the telnet protocol. However, very few devices use telnet these days. Its use is not recommended for security reasons.
Telnet sends all user names and passwords in the clear. It is very easy to listen to network traffic and steal user names and passwords from telnet traffic. By mid-1990s, such password sniffing attacks had become the largest security problem on the Internet. That was the very problem SSH was designed to solve. Compromised routers, switches, or ARP proofing attacks can also be used to inject arbitrary commands into telnet sessions.
There is a separate version of the software, called PuTTYtel, for countries that do not allow any use of encryption. However, SSH is now used in all countries, officially or unofficially. Most systems can no longer be managed without encryption. Even the most oppressive countries need to secure their systems somehow. There cannot be cybersecurity in a networked environment without encryption.
PuTTY also supports connecting to serial ports and raw sockets. These can sometimes be useful for debugging purposes and for working with some legacy devices. For example, in kernel development access via a serial port is still sometimes the best way to debug a panic that causes an immediate reboot, as it provides a way to see the boot messages.
Known security vulnerabilities
Version 0.66 and earlier are known to contain security vulnerabilities. Upgrading to the latest version is recommended.
-
Buffer overflow in SCP. This a potential stack overflow and remote code execution vulnerability. A corrupt server could execute code on the client when any file is downloaded. It could also be exploited by man-in-the-middle attacks.
-
Integer overflow in terminal escape sequence handling. This is a memory corruption and possible remote code execution vulnerability. It involves sending an escape sequence to the terminal. For example, a compromised switch could inject the attack into a session. It can also be exploited by a corrupt server to execute code on the client, or using man-in-the-middle attacks.
Lack of proper key management can expose servers to risk and allow attackers to spread server-to-server or jump through desktops/laptops containing SSH keys. More information on SSH key management can be found here.
History and maintenance status
PuTTY is one of the oldest SSH clients for Windows. It was first released by Simon Tatham in 1998. SSH support was added in 2000.
After 19 years, the software is still a beta version. Development has been slow, but it is still being maintained. A recent version added support for elliptic curve cryptography. The user interface or features have not changed much in 15 years.
A Frequently Asked Questions document (FAQ) can be found here.
Where to find the source code
Source code is available on Simon Tatham's home page. Installation packages can be downloaded securely here.
Extensions, branches, and integrations
The product is open source. Several projects have branched off and build on its source code.
-
PuttyManager is a tabbed user interface, but development appears to have stopped years ago.
-
ExtraPuTTY is a fork that has various extensions, such as Lua programming language integration.
-
MTPuTTY is a version of with a user interface that supports multiple tabs (i.e., a tab control where each tab is a terminal window).
-
WinSCP has some level of integration for file transfer functionality.
Videos and screenshows
Tutorial video
Terminal window
SFTP client