What is the Internet of Things (IoT) & the IoT Security?
Contents
What Is the Internet of Things? IoT Security and Risks IoT Breach Examples What Can the Society Tolerate? How Will the Society Solve It? Minimum Acceptable Level of Security How Does a Typical IoT Attack Work? How Does the Attack Penetrate a Device? Back-End Servers in the Cloud Field Service Access Medical Device Security Research Tool to Find Vulnerable Connected ThingsWhat Is the Internet of Things?
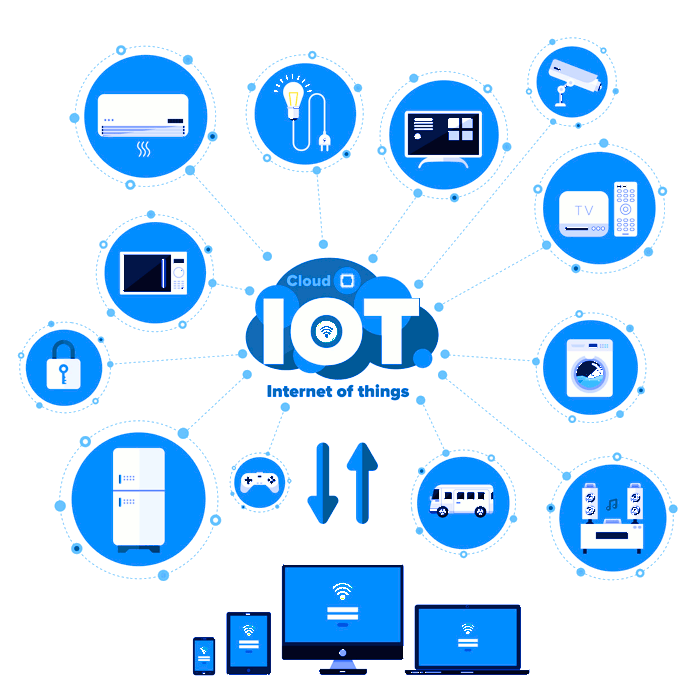
IoT (Internet of Things) refers to devices that are connected to the Internet. It is a very varied field, with the devices ranging from lightbulbs and switches to cameras, printers, cars, and heavy industrial machinery. The number of such devices is expected to grow to tens of billions in a few years. It is also related to digitalization, which is one of the megatrends driving higher productivity in the industry.
Many connected devices are sold to consumers and used at home. Others are used in offices. Yet others are used in the industry or logistics. Smart cities and smart power grids are bringing the degree of connectedness to a whole new level.
IoT Security and Risks
Security is a major limiting factor for IoT. There will be a staggering number of such devices, and some of them perform functions that can cause loss of life or disrupt important functions of the society.
Many of the first-generation devices have default passwords that are shared by all devices. Many contain design flaws that allow attackers to take full control of the devices. We have seen several attacks where the number of IoT devices taken under control has been in the millions.
A major security concern arises from the sheer number of the devices. They can be programmed to send traffic to a particular destination. When millions of devices do the same simultaneously, even the best connected sites in the world become so congested they can no longer operate. This is called a Distributed Denial-of-Service Attack, or DDoS.
Many connected devices also come with cameras and microphones. They have already been used by both criminals and intelligence agencies to snoop on individuals. Smart TVs are particularly lucrative for this, as they are often centrally placed in apartments, many come with microphones and cameras, and a recent study found that 85% of current smart TVs could be hacked over the TV broadcast channel. The CIA (US Central Intelligence Agency) has been reported to already have used Smart TVs for espionage.
IoT Breach Examples
Some examples of recent IoT breaches include:
-
Report: Millions (and Millions) of Devices Vulnerable in latest Mirai Attacks
-
IoT eminently hackable – 900,000 routers down and millions vulnerable
-
World's Biggest Mirai Botnet Is Being Rented Out for DDoS Attacks
-
Tesla Responds to Chinese Hack with a Major Security Upgrade
-
Infected Android phones could flood America's 911 with DDoS attacks
-
Over 85% Of Smart TVs Can Be Hacked Remotely Using Broadcasting Signals
-
DDoS Attack Takes Down Central Heating System Amidst Winter In Finland
Every day, companies and services are faced with DDoS attacks of unprecedented magnitude. It is only going to get worse as devices from toothbrushes to toasters to fridges to televisions become widely sold and exploited.
What Can the Society Tolerate?
People will eventually be injured and die as a result of IoT attacks. Cars will drive off the road; millions might watch their houses freeze while heating contractors are flooded with bogus calls; and emergency calls won't go through to get an ambulance to a heart attack or car crash victim.
In many cases, the connected devices are very badly designed from a security viewpoint. Manufacturers make design choices that are known to make the devices vulnerable. Attackers may render the devices vulnerable, may use them to conduct illegal activity (including drug dealing and terrorism) making the traffic look like it comes from ordinary people's homes, and may cause life-threatening harm to the society. It is not a theoretical posibility; it is happening all the time.
Eventually the society will not take it any more.
How Will the Society Solve It?
There are several ways the society might approach the problem.
-
Outright ban on IoT. Not likely, because they are useful and important for economic productivity via digitalization.
-
Regulations on minimum level of security, perhaps combined with certification.
-
Product liability, personal injury, or wrongful death litigation and resulting substantial civil liabilities.
-
Liability insurance companies requiring a certain level of security (possibly combined with certification) to provide liability insurance or to give lower premiums.
-
Technical solutions that mitigate the impact of attacks. However, DDoS attack and phone call flooding mitigation is really hard, and even small-scale attacks like committing serious crimes through other people's Internet connections can be quite harmful to the parties involved. It is unlikely that technical solutions alone will solve the problem.
Minimum Acceptable Level of Security
One very possible approach will be defining a minimum acceptable level of security for consumer IoT devices. The requirement could be driven by legal liability, insurance, or regulation. Products that meet the acceptable level would be safer from liability claims than those that blatantly disregard basic security controls and sell products that can be reasonably expected to cause unnecessary serious harm to others.
The minimum standard would likely to be a moving target, with the bar rising as new vulnerabilities are found and the worst ones have been addressed.
Key elements of the minimum acceptable security controls would include:
-
No default passwords that are the same for many devices. If passwords are used, an acceptable practice would be to manufacture each device with a unique password and print it on a sticker attached to the bottom of the device.
-
A way of practically getting nearly all deployed devices upgraded in reasonable time - in many cases without consumer intervention. This would probably mean automated upgrades being enabled by default.
-
A web user interface and overall operating system design that does not let latest versions of standard automated penetration testing suites to break in.
-
No unnecessary services accessible from the Internet.
-
No plaintext passwords (e.g., no telnet).
-
Proper management of trusted roots and certificates.
-
Secure communications protocols, such as TLS (Transport Layer Security) or SSH.
-
Proper source randomness for encryption keys - preferably a hardware random number generator.
How Does a Typical IoT Attack Work?
In a typical attack, the attacker gains control of an Internet-connected device using any of several means. Once the device is under control, the attacker installs additional software on the device. The device is then enlisted to perform further attacks or is used for the attacker's purposes.
Often the whole process is automated, and hacked devices are used to attack other devices. The devices often take commands from one or more command-and-control centers, which are typically just other devices on the Internet.
Sometimes access to thousands of hacked devices is sold for nefarious purposes. Such collections of devices are often called botnets.
How Does the Attack Penetrate a Device?
In principle, any cyberattack can be used to penetrate a device. Some of the most common are:
-
Default passwords configured by the manufacturer that the user never changed.
-
Easily guessable passwords that the attacker tries, and often succeeds.
-
Well-known vulnerabilities in software that haven't been patched. Many IoT devices are never upgraded and consumers don't know to or how to upgrade them. Besides, who wants to be upgrading their toaster or fridge all the time?
-
Basic Web user interface design flaws.
-
Basic flaws in an authentication sequence.
-
Flaws in key management, such as in verifying the authenticity of upgrades.
Back-End Servers in the Cloud
Many IoT devices also connect to back-end systems, such as cloud servers. Some devices are paired with mobile phones, so that they can be controlled remotely. These techniques require the use of secure cryptographic protocols to be secure. They must be properly designed. They also require managing cryptographic keys and trusted certification authorities.
There are also many privacy issues involving data sent to such back-end systems. The data often carries a wealth of sensitive information related to location, activity, health, presence, and capacity of individuals, groups, and employees, in both public and private facilities. It may also be subject to regulations such as HIPAA or EU GDPR (General Data Protection Regulation).
Field Service Access
In many heavier Internet-connected devices, the manufacturer wants to collect data about the device's operation for preventative maintenance, licensing, and service operations. Often, the customer's field service organization logs into the device. Sometimes these devices cost many millions of dollars and can cause substantial damage if a malicious party gains control. Examples include paper mills, mining machinery, and harbor cranes.
Generally, security for high-end devices is driven by the cost of process failures, local physical damage that the devices could cause, environmental impact that malfunctions could have, or immediate risk to human life.
Medical Device Security
Medical device security is of particular concern, as such devices often perform life-critical functions.
For medical devices, the bar on minimum acceptable controls must be much higher than consumer devices. A single medical device may kill or injure a person, while usually a single consumer devices only cause loss of privacy or risk to property. Millions of consumer devices, however, can collectively be just as dangerous as a medical device - or even more so.
Research Tool to Find Vulnerable Connected Things
Shodan is a service for finding IoT devices on the Internet. It is targeted for researchers, but can be used for all sorts of purposes from market research to finding vulnerable devices to target in attacks. It now also has a feature for finding cameras known to be vulnerable.