SSH Protocol – Secure Remote Login and File Transfer
This page is about the SSH protocol. For the company behind it, see SSH Communications Security. For using the Linux ssh command, see ssh command usage. For SSH clients, servers, and technical information, see SSH (Secure Shell) home page.
The SSH protocol (also referred to as Secure Shell) is a method for secure remote login from one computer to another. It provides several alternative options for strong authentication, and it protects communications security and integrity with strong encryption. It is a secure alternative to the non-protected login protocols (such as telnet, rlogin) and insecure file transfer methods (such as FTP).
Contents
Typical uses of the SSH protocol How does the SSH protocol work Strong authentication with SSH keys SSH provides strong encryption and integrity protection IETF SSH standard and detailed technical documentation The core protocol SFTP file transfer protocol Public key file format How to Cite SSHTypical uses of the SSH protocol
The protocol is used in corporate networks for:
-
providing secure access for users and automated processes
-
interactive and automated file transfers
-
issuing remote commands
-
managing network infrastructure and other mission-critical system components.
How does the SSH protocol work
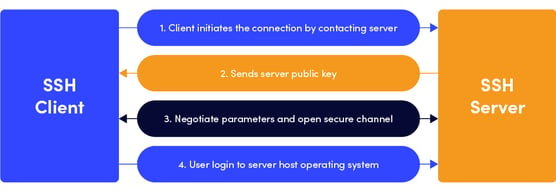
The protocol works in the client-server model, which means that the connection is established by the SSH client connecting to the SSH server. The SSH client drives the connection setup process and uses public key cryptography to verify the identity of the SSH server. After the setup phase the SSH protocol uses strong symmetric encryption and hashing algorithms to ensure the privacy and integrity of the data that is exchanged between the client and server.
The figure below presents a simplified setup flow of a secure shell connection.
Strong authentication with SSH keys
There are several options that can be used for user authentication. The most common ones are passwords and public key authentication.
The public key authentication method is primarily used for automation and sometimes by system administrators for single sign-on. It has turned out to be much more widely used than we ever anticipated. The idea is to have a cryptographic key pair - public key and private key - and configure the public key on a server to authorize access and grant anyone who has a copy of the private key access to the server. The keys used for authentication are called SSH keys. Public key authentication is also used with smartcards, such as the CAC and PIV cards used by US government.
The main use of key-based authentication is to enable secure automation. Automated secure shell file transfers are used to seamlessly integrate applications and also for automated systems & configuration management.
We have found that large organizations have way more SSH keys than they imagine, and managing SSH keys has become very important. SSH keys grant access as user names and passwords do. They require a similar provisioning and termination processes.
In some cases we have found several million SSH keys authorizing access into production servers in customer environments, with 90% of the keys actually being unused and representing access that was provisioned but never terminated. Ensuring proper policies, processes, and audits also for SSH usage is critical for proper identity and access management. Traditional identity management projects have overlooked as much as 90% of all credentials by ignoring SSH keys. We provide services and tools for implementing SSH key management.
SSH provides strong encryption and integrity protection
Once a connection has been established between the SSH client and server, the data that is transmitted is encrypted according to the parameters negotiated in the setup. During the negotiation the client and server agree on the symmetric encryption algorithm to be used and generate the encryption key that will be used. The traffic between the communicating parties is protected with industry standard strong encryption algorithms (such as AES (Advanced Encryption Standard)), and the SSH protocol also includes a mechanism that ensures the integrity of the transmitted data by using standard hash algorithms (such as SHA-2 (Standard Hashing Algorithm)).
IETF SSH standard and detailed technical documentation
The core protocol
When the SSH protocol became popular, Tatu Ylonen took it to the IETF for standardization. It is now an internet standard that is described in the following documents:
RFC 4251 - The Secure Shell (SSH) Protocol Architecture
RFC 4253 - The Secure Shell (SSH) Transport Layer Protocol
RFC 4252 - The Secure Shell (SSH) Authentication Protocol
RFC 4254 - The Secure Shell (SSH) Connection Protocol
SFTP file transfer protocol
The SFTP (SSH File Transfer Protocol) is probably the most widely used secure file transfer protocol today. It runs over SSH, and is currently documented in
Public key file format
The public key file format is not a formal standard (it is an informational document), but many implementations support this format.
RFC 4716 - The Secure Shell (SSH) Public Key File Format
How to Cite SSH
To cite SSH in a research paper, please use the following:
Tatu Ylonen: SSH - Secure Login Connections over the Internet.
Proceedings of the 6th USENIX Security Symposium, pp. 37-42, USENIX, 1996.