SSH File Transfer Protocol (SFTP): Get SFTP client & server
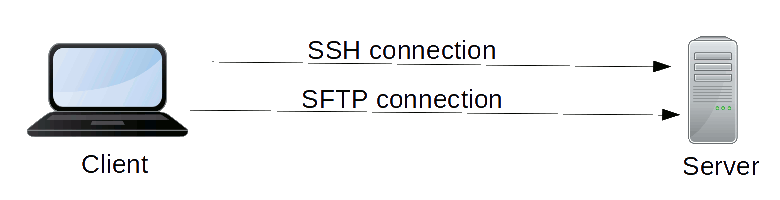
SFTP (SSH File Transfer Protocol) is a secure file transfer protocol. It runs over the SSH protocol. It supports the full security and authentication functionality of SSH.
SFTP has pretty much replaced legacy FTP as a file transfer protocol, and is quickly replacing FTP/S. It provides all the functionality offered by these protocols, but more securely and more reliably, with easier configuration. There is basically no reason to use the legacy protocols any more.
SFTP also protects against password sniffing and man-in-the-middle attacks. It protects the integrity of the data using encryption and cryptographic hash functions, and autenticates both the server and the user.
Contents
SFTP Port Number SFTP Client for Windows and Mac SFTP Server for Linux, Windows, and Mac SCP Command on Linux SFTP Command on Linux SSHFS & Using SFTP for File Sharing Interactive and Automated Secure File Transfers Commercial File Transfer Solutions using SFTP SFTP Libraries for Developers SFTP Protocol SFTP vs. FTPS SFTP screenshotSFTP Port Number
SFTP port number is the SSH port 22 (follow the link to see how it got that number). It is basically just an SSH server. Only once the user has logged in to the server using SSH can the SFTP protocol be initiated. There is no separate SFTP port exposed on servers. No need to configure another hole into firewalls.
SFTP Client for Windows and Mac
Many SFTP client implementations are available. Many SSH clients support SFTP.
SFTP Server for Linux, Windows, and Mac
SFTP server usually comes as part of an SSH implementation. Most organizations use either Tectia SSH or OpenSSH as the server; both come with SFTP server implementations out-of-the-box.
SCP Command on Linux
The scp command is a file transfer program for SFTP in Linux. The scp command line interface was designed after the old rcp command in BSD Unix. The scp also usually comes with the OpenSSH package.
Its typical use is:
scp [-r] file ... [user@]host:[path]Basically, this copies one or more files to the given host. If user is given, then they are copied to that account on the host. If no user is supplied, then the same user name as on the client side is assumed. If path is given, then the files are copied to that directory (relative to the given user's home directory). If no path is given, the files are copied to the user's home directory. If the -r option is supplied, then files may be directories, and the given directory and all its subdirectories and files in them (recursively) are copied.
One can also copy in the reverse direction:
scp [-r] [user@]host:file pathCommonly, the path would be ., i.e., the current directory.
SFTP Command on Linux
The sftp command in Linux is a client program for SFTP. The sftp command line interface was designed to be similar to the ftp command. The sftp command is typically part of the OpenSSH package.
SSHFS & Using SFTP for File Sharing
SFTP can furthermore be used for file sharing, similar to Windows file sharing and Linux NFS. The main difference is that SFTP is secure, and can be used reliably over Network Address Translation (NAT) and the public Internet.
Sshfs is a network file system for Linux that runs over the SFTP protocol. It can use any SSH server as a server, and use remote files over the network as if they were local files. The remote file system can be mounted and unmounted as desired. It is the most convenient way to mount remote files ad hoc, without the need for any configuration by the server administrator. SSH keys can even fully automate establishing the connection to the server. Basically, anyone who is able to log into the server can mount its file system, with access to those files the user has access to.
Other file sharing implementations using SFTP include:
 Interactive and Automated Secure File Transfers
Interactive and Automated Secure File Transfers
Like SSH itself, SFTP is a client-server protocol. SFTP clients are included in quality SSH clients and complete enterprise grade SSH implementations provide both SFTP client and server functionality. Some SSH clients, such as Tectia SSH, also provide graphical file manager views into remote filesystems.
On Linux, SFTP is often used as a command-line utility that supports both interactive and automated file transfers. Public key authentication can be used to fully automate logins for automated file transfers. However, proper lifecycle management of SSH keys is important to keep access under control.
Common use cases for automated file transfers include nightly system backups, copying data to disaster recovery systems, distributing configuration data, and moving transaction logs to archival systems. Many organizations have thousands of daily SSH transfers. In come cases, we have seen over 5 million daily automated SSH logins.
Commercial File Transfer Solutions using SFTP
Some commercial file transfer products supporting SFTP include the following. Nothing on this page should be taken as an endorsement of any product or solution.
SFTP Libraries for Developers
There are many open source SSH libraries available for various programming languages.
-
pysftp is a Python implementation
-
Paramiko is another Python implementation
-
pkg/sftp is a Go language implementation
-
libssh is a C implementation of the protocol
-
libssh2 is another C implementation of the protocol
-
Rebex SFTP is a .NET (C#) implementation
-
phpseclib is another PHP implementation
-
SmartFTP is an ActiveX component
-
JCraft JSch is a Java implementation
-
SSHJ is another Java implementation
-
Comparison of Commons VFS, SSHJ and JSch Libraries for SFTP Support
SFTP Protocol
The SFTP protocol runs over the SSH protocol as a subsystem. It was originally designed by Tatu Ylonen for SSH 2.0 in 1997-1998. There is no separate SFTP port; it uses the normal SSH port.
The protocol supports multiple concurrent operations. Each operation is identified by a unique number assigned by the client, and servers response contains the same identifying number. Server may process requests asynchronously and may return responses out-of-order. For performance reasons, file transfer clients often send multiple requests before stopping to wait for responses.
Operations or packet types supported by the protocol include:
INIT: sends client version numbers and extensions to the server
VERSION: returns server version number and extensions to the client
OPEN: opens or creates a file, returning a file handle
CLOSE: closes a file handle
READ: reads data from a file
WRITE: writes data to a file
OPENDIR: opens a directory for reading, returning a directory handle
READDIR: reads file names and attributes from a directory handle
MKDIR: creates a directory
RMDIR: removes a directory
REMOVE: removes a file
RENAME: renames a file
STAT: returns file attributes given a path, following symlinks
LSTAT: returns file attributes given a path, without following symlinks
FSTAT: returns file attributes given a file handle
SETSTAT: modifies file attributes given a path
FSETSTAT: modifies file attributes given a file handle
READLINK: reads the value of a symbolic link
SYMLINK: creates a symbolic link
REALPATH: canonicalizes server-size relative path to an absolute path
The following response packets are returned by the server:
STATUS: indicates success or failure of an operation
HANDLE: returns a file handle upon success
DATA: returns data upon success
ATTRS: returns file attributes upon success
There is also an extension mechanism for arbitrary vendor-specific extensions. The extensions that are supported are negotiated using the INIT and VERSION packets.
EXTENDED: sends a vendor-specific request from client to server
EXTENDED_REPLY: sends a vendor-specific response from server to client.
SFTP vs. FTPS
People often want to compare SFTP vs. FTPS. FTPS is basically the old ftp protocol run over SSL (Secure Sockets Layer) or TLS (Transport Layer Security).
Benefits of SFTP over FTPS include:
-
SFTP runs over SSH in the standard SSH port. Thus, no additional ports need to be opened on the server and no additional authentication needs to be maintained. This simplifies configuration and reduces the likelihood of configuration errors.
-
FTPS needs complicated firewall configuration and may not work over NAT. Ports 989 and 990 need to be open. Furthermore, FTPS supports both active and passive modes (see FTP), which further complicates firewall configurations and is prone to problems.
-
FTPS requires an X.509 certificate for the server, typically from a public certificate authority. SSH works without any centralized infrastructure. SFTP can utilize whatever host key distribution or certification method is in use for SSH, without needing additional work and ongoing maintenance.
-
FTPS is basically FTP, which means it has ASCII mode, which can corrupt files if the mode is not properly set. Some implementations default to ASCII mode.
-
FTPS cannot be used as a file system. (This does not improve security, as it can still read the same files.)
-
FTPS requires an extra server software package to be installed and patched, whereas SFTP usually comes with SSH with the system.
SFTP screenshot