Malware & Hackers Collect SSH Keys to Spread Attack
SSH keys are access credentials that grant access to servers without having to type a password. They are commonly used for automated machine-to-machine access for file transfers and integration of information systems. Unix and Linux system administrators use them every day.
Advanced malware and hackers have been collecting SSH keys for years. This is for a few reasons:
-
The keys provide a long-term backdoor, and they can be used to spread the attack from one server to another - possibly across nearly all servers in an enterprise, including disaster recovery data centers and backup data centers.
-
The keys often grant access to credit card payment environments and financial data environments in public companies.
-
The keys commonly provide root or administrator access, thus allowing installation of malware, compromising of software, or even outright destruction.
Hackers have known about SSH keys for years. We have talked to a former government hacker, now a penetration tester, who said he would always first get all SSH keys. In the famous Sony breach, hackers stole SSH credentials and apparently used them to attack. Authentication credentials, particularly SSH keys, are a natural target for attackers.
Contents
Malware Using SSH Keys Spreading Using SSH Keys What Can Malware and Their Masters Do with the Keys and Access Productized Malware - Tools for Criminals How Hackers Gain Access to Intranet Even when Protected by Firewalls What to Do?Additional Links
Malware Using SSH Keys
The first publicized malware to collect SSH keys was Careto, discovered in 2014 and believed to be the work of a nation state. There have also been many other instances of malware collecting SSH keys and/or otherwise leveraging SSH for attacks:
-
New Linux/Rakos threat: devices and servers under SSH scan (again)
-
BlackEnergy by the SSHBearDoor: attacks against Ukrainian news media and electric industry
-
DDoS Malware for Linux Distributed via SSH Brute Force Attacks
-
MMD-0047-2015 - SSHV: SSH bruter ELF botnet malware w/hidden process kernel module
The list above is far from exhaustive, and many more SSH-using malware packages and modules are likely to exist for systems that are used by cybercriminals, militaries, and intelligence agencies.
SSH keys are often used for copying data into backup systems and disaster recovery data centers. They are also often used for reconfiguring various routers and systems when switching to using a disaster recovery data center. This means that SSH keys can commonly be used to spread an attack to these systems, unless the transitive access graph has been carefully thought out.
Spreading Using SSH Keys
We have found that most large organizations have many times more SSH keys than they have servers or user accounts. For example, in one typical financial institution we found 3 million SSH keys granting access to 15,000 servers. That is an average of 200 keys per server.
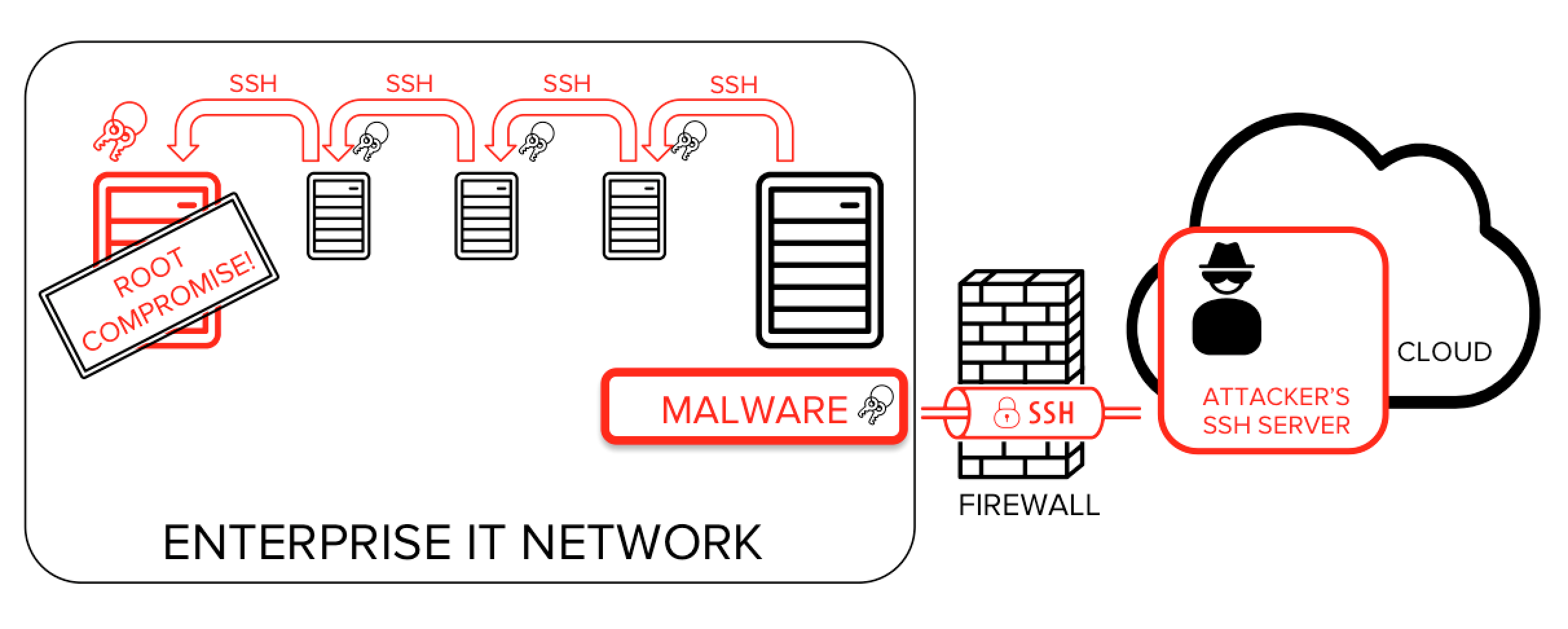
Once an attacker breaks into one server, it is highly likely that the attacker will find one or more private keys from that initial server. The attacker can then use these discovered private keys to login to other servers - typically more than one - and again find private keys from these servers. Repeating this quickly spreads the breach and exposes more and more of the target network.
Leveraging unmanaged SSH keys allows the attacker to establish and expand a foothold in the target networks, and an attack like this may quickly spread through almost the whole environment.
What Can Malware and Their Masters Do with the Keys and Access
Once the attackers are in possession of SSH keys that grant access to a system, they gain operating system level access to the system, typically a command line. In our analysis of real-life deployments, we have seen that roughly 10% of all SSH keys grant root access. For the attackers root privileges allow unrestricted access to all aspects of the system. In cases where the SSH keys allow non-root access, the attackers will typically attempt to combine local attacks, using vulnerabilities in software and/or operating system on the server, to escalate privileges to root.
Once an attacker has gained root access, anything is possible. The attacker can modify the operating system, install malware into the BIOS or firmware (e.g., a form of virtualized rootkit), modify the operating system or any services running on it. The attacker can even damage the system and its data beyond repair by wiping the BIOS, hard drive firmware, and network adapter firmware. Root access typically gives the attacker total control of the system.
Even without root access, the attackers can read and modify any data accessible to the account(s) they have access to. For example, access to an Oracle database service account may grant direct read and modify access to the raw database files and to the memory of the database server process, bypassing all database-level logging, security controls, and integrity checks. This allows extracting data, subverting encryption, inserting fraudulent data, or damaging or destroying the database.
An attack that uses SSH keys to spread throughout an enterprise could take the target down for months. Or a country, if targeting its critical infrastructure.
Productized Malware - Tools for Criminals
Penetration testing tools, such as Cobalt Strike/Armitage include modules for exploiting SSH keys in attacks. These tools are highly productized and easy to use. They automate some of the manual tasks involved in attacks. They have been designed to be easy enough to be used even by people without extensive technical knowledge. The existence and design of these tools indicate the high value of SSH keys as targets. Actual attack tools perform similar attacks much more stealthily.
SSH keys are valuable. In one public instance, a key was sold for 50 Bitcoints and used to penetrate into an organization and steal Bitcoins from a cryptocurrency exchange. The extent of the black market for stolen SSH keys (and back-tunneling ports into respective intranets) is currently not known. A known fact is that certain government sites receive constant attacks where various SSH keys are tried against them. The attackers are trying to pick the lock with keys they have acquired.
How Hackers Gain Access to Intranet Even when Protected by Firewalls
Using SSH keys requires a TCP/IP connection to to the server. A common misconception is that the problem would not be so serious in the internal networks as it is on the public Internet. This is a false assumption for a couple of reasons:
-
Attackers are often already inside the protected network (either in person, via a connection, or using malware). There have been many cases where SSH keys have been stolen, sold, or misused by employees.
-
Attackers commonly leverage port forwarding. Most firewalls are unable to prevent this, and those that do, have very limited functionality.
What to Do?
Risks related to poorly managed SSH keys can be greatly reduced by proper access provisioning and termination processes, deployment of key management tools, and regular audits.
-
NIST IR 7966 is US Government best practice guidelines for addressing SSH keys.
-
Our SSH key management page contains additional information about risks, the process, and how to approach SSH key management projects.
-
Read about compliance requirements related to SSH keys.
-
SSH Risk Assessment is a fast, low-cost service that helps quantify and evaluate an organization's SSH key management state and related risks.
-
Universal SSH Key Manager® is the leading tool for addressing SSH key management - discovery, lock-down, remediation, monitoring, and establishing efficient provisioning and termination processes for keys. It enables application teams to take ownership of incoming and outgoing access in their information systems, gives security teams overall visibility over the environment, and facilitates smooth audits.
In addition, it is important to control SSH port forwarding into the organization, as it makes utilizing stolen keys and otherwise breaking into the organization frighteningly easy.
Additional Links

