FTP Client – basic (insecure) file transfer capability
This page presents an overview of an FTP client and explains how SFTP provides the same functionality but securely and more robustly, and is easier to use and configure.
Contents
FTP Client Overview FTP Is Vulnerable to Identity and Data Theft SFTP Is a Secure Alternative to FTP Tectia SSH Clients and ServersFTP Client Overview
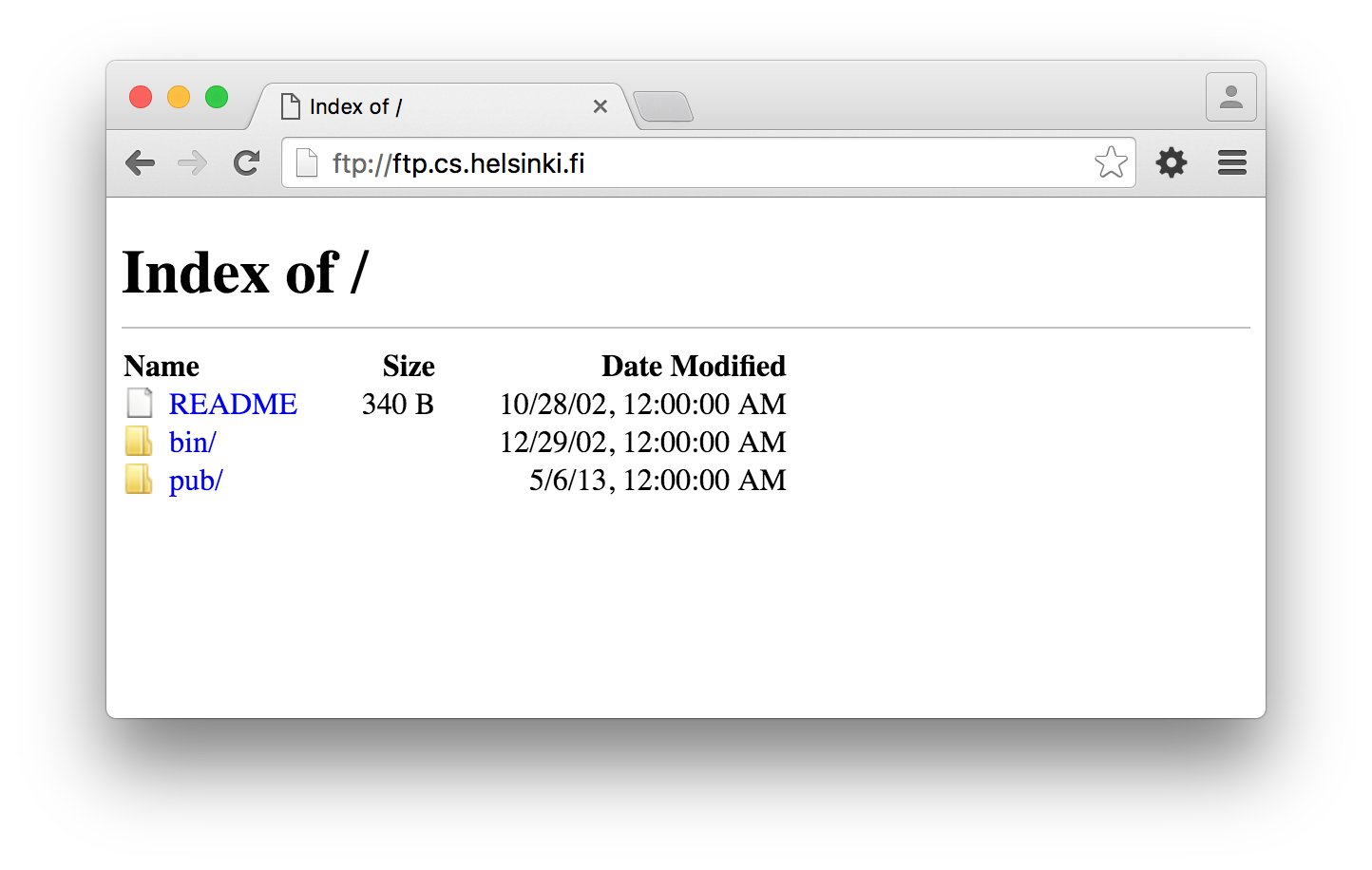
An FTP client is a software application that allows logging in to a computer that runs FTP server software. Once a user has connected to a server and authenticated using a password, the user can then transfer files and folders to and from the server computer. The client functionality is embedded in most common web browsers, but is also available as a separate, dedicated software application for most common operating systems.
FTP Is Vulnerable to Identity and Data Theft
The FTP protocol is unencrypted and transmits passwords and data in the clear. Tools are widely available for capturing user names and passwords from the network. This is called password sniffing, and was a common attack already in the mid-1990s.
SFTP Is a Secure Alternative to FTP
The SFTP protocol and SSH have replaced FTP in practically all new applications. FTP should only be used with legacy systems that do not support SFTP. It is generally impossible to achieve compliance in regulated industries when using FTP.
With the SFTP alternative, it is also easy to automate file transfers. SFTP supports the use of cryptographic keys, SSH keys, for authentication. This makes automation very easy.
The SFTP protocol also works across firewalls and Network Address Translation (NAT) automatically and without any special configuration.
Tectia SSH Clients and Servers
See the separate SSH client page for alternatives for a file transfer client.
As a replacement for an FTP server, we recommend Tectia SSH Server. It is available for Windows, Unix, Linux, and z/OS.