We had our 2021 Customer Advisory Board (CAB) event just a while ago. This year, the CAB was organized virtually and was attended by more than 30 customers from the EMEA region. The participants represented leading European organizations in financial services, manufacturing, IT services, and transportation, among others. The full-day event gave the attendees an opportunity to hear from industry experts and SSH.COM’s technology teams as well as share user experiences and feedback on solution implementation and best practices.
Digital keys: needed but dangerous if left unmanaged
Rami Raulas, Head of EMEA Sales, opened the event by giving an overview of the current cybersafety environment and SSH.COM’s role in it. Mr. Raulas discussed how tightening regulation and compliance requirements, on one hand, and ever-increasing risk factors on the other, drive companies to opt for secure, automated, and productivity-enhancing access management solutions.
Reportedly, 74% of cyber breaches start with digital keys being in the wrong hands. One of the leading themes of the day was the‘passwordless future’. According to a live poll, 64% of the participants deemed it a ‘must-have’ or ‘very important’ to avoid the hassle of managing passwords going forward.
The event keynote was delivered by Martin Kuppinger, Principal Analyst from KuppingerCole, Europe’s leading Analysts on the topics of Information Security in the era of Digital Transformation. Mr. Kuppinger’s presentation, titled ‘Too many PAM’s out there – Finding your path through the jungle of PAM approaches’ highlighted the complexity of choice in the privileged access management solutions. The topic is particularly timely because the use cases for PAM are expanding, with industrial automation access (Operational Technology) as a prime example.
One PAM for all use cases?
Many of the available PAM solutions have an ever-increasing list of features, but it is rarely the case that one solution will be ideal for every possible use case. Instead, Mr. Kuppinger suggested that organizations approach the issue by first reviewing what shall be managed (e.g., sessions, entitlements, and secrets) and where they shall be managed (servers, applications, devices, etc.).
As an example, a PAM solution for DevOps and Cloud use cases should take into account the realities of the hybrid IT environments, not be tied to a specific cloud vendor, and be flexible in its deployment. A successful PAM deployment should not only support the reality of the current IT environment, but also take into account the future that is increasingly built on cloud and SaaS platforms.
Learn more about KuppingerCole's views on DevOps PAM in this white paper.
Digital keys, access secrets and how to handle them with care?
Following the keynote, a panel discussion focused on the emerging trends in privileged access management. Many organizations are starting PAM implementation projects, and as a consequence, there is increasing demand for modern approached to privileged access, such as Zero Trust, Just-In-Time (JIT), and Just Enough Access (JEA).
However, the transition from standing privileges and shared admin accounts to the more secure Zero Trust approach is a journey and requires a carefully planned approach, in addition to a modern PAM solution.
Among the highlights of the CAB, several customers shared their experiences with SSH.COM's leading solutions PrivX, a lean ‘Zero Trust’ PAM based on ephemeral certificates, and Universal SSH Key Manager (UKM). PrivX was praised for its good fit for modern hybrid cloud environments, as well as ease of implementation thanks to automated onboarding of target assets and user identities. Access to Operational Technology (OT) resources was also discussed as an emerging requirement in the industrial manufacturing sector.
Long-term users of UKM shared insights on how the solution has reduced the complexity and security gaps of managing environments with tens of thousands of target host and millions of individual keys. One of the primary takeaways was that ensuring a successful implementation in such extensive environments takes careful planning and close cooperation with the customer and SSH.COM’s engineering team. Furthermore, improvement opportunities were discussed, including the expansion of API support and usability enhancements.
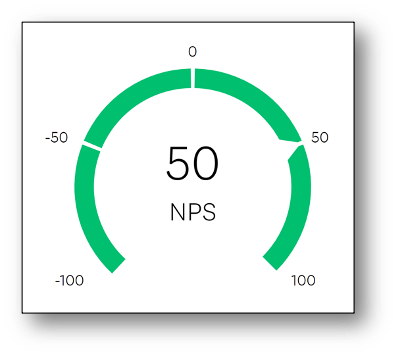
Amidst the interactive sessions, PrivX’s product manager Esa Tornikoski highlighted the key features of the product, while giving his take on why customers have given PrivX an industry-leading NPS score of 50. Shifting focus into the future, Mr. Tornikoski presented a short-term feature development roadmap and longer-term R&D directions, including enhancements for Secure Cloud Access, M2M/A2A, OT/IoT as well as traditional Interactive PAM functionalities. In particular, Secure Cloud Access was chosen as a primary area of interest by the attendees.
 Built together with customers
Built together with customers
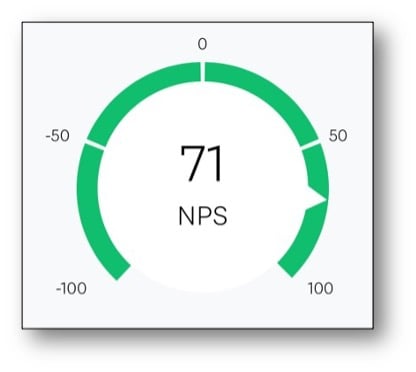
UKM’s product manager Marieta Uitto opened her presentation by revealing the latest (and greatest) NPS score 71, owing to the long-standing and close collaboration with UKM’s users. Ms. Uitto also showcased the 2021 feature roadmap and took questions from the audience.
 To top things off, David Wishart, VP Partnerships, discussed the recently initiated integration efforts of PrivX and UKM – dubbed PrivX Discovery and UKM Zero Trust. The upcoming products will help customers to, e.g., gain visibility and control in the PAM use case and eliminate the need to keep adding SSH keys into IT environments with increasing M2M access requirements. According to the attendees, encryption keys are still the most important elements of secrets management, followed by SSH keys and passwords.
To top things off, David Wishart, VP Partnerships, discussed the recently initiated integration efforts of PrivX and UKM – dubbed PrivX Discovery and UKM Zero Trust. The upcoming products will help customers to, e.g., gain visibility and control in the PAM use case and eliminate the need to keep adding SSH keys into IT environments with increasing M2M access requirements. According to the attendees, encryption keys are still the most important elements of secrets management, followed by SSH keys and passwords.
In conclusion, the event was a success and according to a poll held during the event, 90% of attendees voted that the event was “very valuable”. As one attendee put it,
“The event was very interesting. I’m glad to see your roadmap is flowing with enhancements and your clients thrive using your solution. It really makes me feel we made a good choice working with you”.
Did you miss the event? Want to know more? Get in touch with us to get your private session on how to get control and automate your digital keys to increase your productivity.
More resources: