Did you know that something as trivial-sounding as granting access for your developers or third parties to a product development environment can throw a gorilla-sized monkey wrench into your operations and productivity?
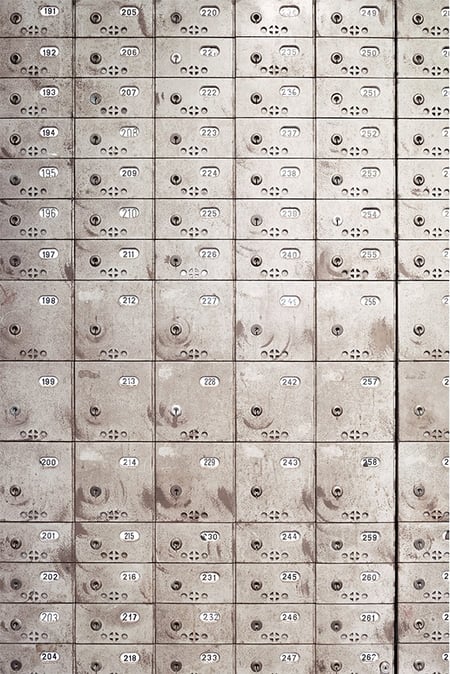
It’s all about a select group of people: those who have access to mission-critical data and those who manage that access. These people are often referred to as power users or privileged users, who are prime targets for any scam aiming to exploit their elevated access rights. With traditional privileged access management (PAM) solutions, you grant that access to a resource per user and per host. And therein lies the problem.
By 2025, the world will need to secure 338 billion lines of new software code, up from 111 billion lines in 2017. This represents a 15% year-over-year growth in new code that developers must protect. Such staggering figures underscore the need for a more robust, flexible approach to access management—a need that traditional PAM systems are ill-equipped to meet.
This is where Super Lean Access Management (SLAM) steps in.
Can you really handle multi-cloud and third parties, PAM?
In the age of the cloud, you have your consultants, third parties, temps, developers, and whatnots who all need secure access with various levels of granularity and for different periods of time. Then you have the ever-mutating multi-cloud environment where virtual server instances are spawned and killed at a moment’s notice.
All this creates a chain of work that is impossible to maintain manually: linking the user identities with the right level of access, configuring the user devices to open that access, and configuring the servers to approve that access. And you have to rinse and repeat if there’s just one change along the way, like a new server, employees changing teams, new devices, or a new security policy.
We’ve already seen the results. Granting access might take up to two days, companies lose visibility into who has access to what resource and with what rights, you have externals running wild and there are leave-behind credentials that are “finders, keepers" — an open season for security breaches.

It’s time to SLAM your PAM!
At SSH.COM, we believe the way to solve the problem is to take the traditional privileged access management functionality but strip it of bloatware and put it on steroids. We’ve designed an access authority that stands between users and hosts and builds a trust relationship between them. It also automates the bulk of access administration work and stays immune to changes in your front-end and back-end.
Today, I’m going to name it, right now, in front of you, just for you: Super Lean Access Management for privileged users (SLAM).
With SLAM, you get user identities from your corporate directory or identity management system (AD/LDAP). Automatically. SLAM!
“At SSH.COM, we believe the way to solve the problem is to take the traditional privileged access management functionality but strip it of bloatware and put it on steroids.”
Those identities are already associated with groups, so all your admin needs to do is to associate those groups with roles that define the power level of access per role. Then, the admin deploys the role configuration to your multi-cloud environment. Once. SLAM!
New users and cloud instances are discovered automatically after that. Your multi-cloud can change, you can scale your host needs up or down, and SLAM just keeps you up-to-date and resilient against potential cyber attacks automatically. SLAM!
The user then logs in via SLAM and instantly gets served the right servers she has access to. She has a view of all her accessible servers. All it takes is one click and she’s in. SLAM!
Did you notice that I didn’t say anything about user-client configuration? It‘s because there isn’t any! This means that the user can change roles, teams, or clients at will and this has no effect whatsoever on ease-of-access – neither does the admin need to manage anything. SLAM!
Say no to password vaults and credentials. SLAM backdoors shut.
With traditional PAM, you have to configure access per user and per host, complicating attack surface management. SLAM is the quiet central authority that checks the legitimacy of access using unique, short-lived access tokens. It always checks that the user is legitimate and that she has the right to access a host at that time, without relying on traditional login credentials. The access is never permanent and stays open only for as long as it has a valid purpose.
“The access is never permanent and stays open only for as long as it has a valid purpose.”
If you remove a user from your AD or LDAP, the connection terminates automatically within 60 seconds. The same is true if the user logs out. You can also define the allocated time for access in advance for external contractors (for example for 12 hours). This means that you never have access to backdoors that stay open indefinitely due to negligence.
Your users don’t exchange USB sticks or SSH keys which are the go-to methods in the traditional world. There are no password vaults that are targets for an attack or passwords that need to be rotated. The session is encrypted but the technology is hidden from the user: it’s there to secure access, not to cause friction. In fact, credentials are not used at all in the traditional sense of the word. SLAM!
What is Super Lean Access Management (SLAM)?
SLAM, an acronym for Super Lean Access Management, represents a fresh approach to managing digital access rights. Unlike traditional Privileged Access Management (PAM) systems, SLAM introduces significant improvements by integrating automation and lean management principles.
The essence of SLAM is its use of automation to handle repetitive tasks efficiently, allowing IT teams to dedicate more time to strategic initiatives rather than routine duties. This automation not only speeds up processes but also reduces the likelihood of human error.
In parallel, lean management in SLAM focuses on stripping away unnecessary procedures, thereby streamlining operations and boosting efficiency. The SLAM method ensures that access rights are granted or revoked through only the most essential steps, maintaining simplicity and effectiveness.
A key distinction between SLAM and conventional PAM systems is their treatment of privileged accounts. Traditional PAM often depends on labor-intensive, error-prone manual processes. SLAM, however, advocates for automation wherever feasible, simplifying processes without adding unnecessary complexity.
Implementing SLAM within your cyber security framework can lead to better operational efficiency by cutting down on manual tasks and improving security. This is achieved through more precise control over access permissions within your network, ensuring that the right people have the right access at the right times.
The Importance of SLAM in Modern Cybersecurity
Every day, we hear about new data breaches or unauthorized access incidents. In this field, the role of Super Lean Access Management (SLAM) is critical.
Why is SLAM so crucial? It directly tackles these modern threats by providing a robust defense. Consider data breaches, a significant risk for any organization. These often stem from inadequate access management systems. SLAM excels here by offering strict control over network access permissions.
Another major threat is unauthorized access. Traditional privileged access management (PAM) systems are riddled with loopholes that hackers, scammers, and other cybercriminals exploit through techniques such as social engineering and phishing emails. SLAM, with its lean, automated approach, effectively seals these vulnerabilities, making unauthorized entries much harder.
Moreover, SLAM's adaptability sets it apart. Unlike traditional PAM solutions, which may falter as cyber threats evolve, SLAM is built to adapt. Its foundational principles support speedy adjustments to meet new challenges or requirements.
In summary, for organizations facing modern cybersecurity issues like data breaches or unauthorized accesses, adopting an adaptable, efficient solution like SLAM could be a game-changer.
Common Challenges and Solutions in Applying the SLAM Method
Implementing the Super Lean Access Management (SLAM) method can present some hurdles. Like any innovation, SLAM introduces unique challenges, one of which is the threat of phishing attacks. These are cyber threats where attackers deceive you into disclosing sensitive information by masquerading as legitimate entities.
For instance, a company might receive an email that seems to be from a trusted sender, requesting login details, email addresses, or other confidential information. This type of attack can escalate to spear phishing, which specifically targets individuals within an organization rather than the broader employee base.
How does SLAM address this risk? By diminishing the reliance on passwords and shared credentials, SLAM reduces the likelihood of falling for these attacks, as there is less sensitive information available for attackers to exploit.
Another significant challenge is the integration of anti-malware solutions with the SLAM framework. Anti-malware tools are essential for identifying and eliminating malicious software from your network, but merging these tools with your access management system can be tricky due to compatibility issues or technical complexities.
The key to overcoming this is automation, a fundamental element of the SLAM approach. Automation facilitates processes such as scanning for malware threats and managing responses automatically, which minimizes human error and boosts efficiency.
However, it's important to remember that deploying any new system demands patience and perseverance, along with continuous monitoring to ensure it performs well over time.
The lean alternative to the PAMdemonium out there
You are thinking about a massive IT project, aren’t you? Remember the bit about stripping down the bloat? We are serious about this.
All it takes is one day to deploy our solution and you are ready to go. If your business needs change, just add a few more cloud instances and you’ve scaled up your privileged access. Our software updates automatically, so you never have obsolete agents with serious security holes in them on the client or the host. That’s maintenance made easy.
You take a huge burden off your access admins’ backs. Your developers can focus on being productive instead of waiting for access. Your cloud set-up, staff roster, and infrastructure in general can change as much as you need. Changes are always just a few clicks away.
The result is that you don’t just “manage access”: you take control of the whole privileged access lifecycle and put your business velocity on overdrive all at once. The best part is that you’ve made operations faster, smoother, and more secure instead of adding complexity. Sometimes you can have it all!
Oh yeah, the bad boy that makes the magic happen is not really called SLAM. It’s called PrivX. Read about its latest features here!
FAQ
How can SLAM help businesses improve their cyber security measures?
SLAM enhances cyber security by providing a streamlined, automated approach to access management, reducing the risk of unauthorized access and simplifying compliance with security protocols.
What is SLAM (Super Lean Access Management) and how does it benefit small businesses?
SLAM is a modern, efficient access management system that simplifies and automates privileged access controls. It benefits small businesses by reducing administrative overhead, ensuring compliance, and enhancing overall security.




